The Security Development Tool is a feature developed initially for AX 2012 that helps to more easily create and maintain security artifacts such as roles, duties, and privileges. Technically this is still a beta tool offered by Microsoft through Life Cycle Services which provides the following features:
- Displays entry point permissions for a given role, duty, or privilege
- Provides the ability to record business process flows and identify the entry points that are used
- Allows for testing a newly created or modified security role, duty, or privilege without having to use a test user account
It is an extremely helpful tool that Security Administrators of AX can use during the development of user security. In Dynamics for 365 Enterprise though, the Security Development Tool doesn’t exist as a separate application but instead its features are implemented directly in the application itself.
Here’s a breakdown of where the features of the Security Development Tool now live in Dynamics 365 Enterprise:
- Full hierarchy view of role, duty, privilege, entry point security assignments
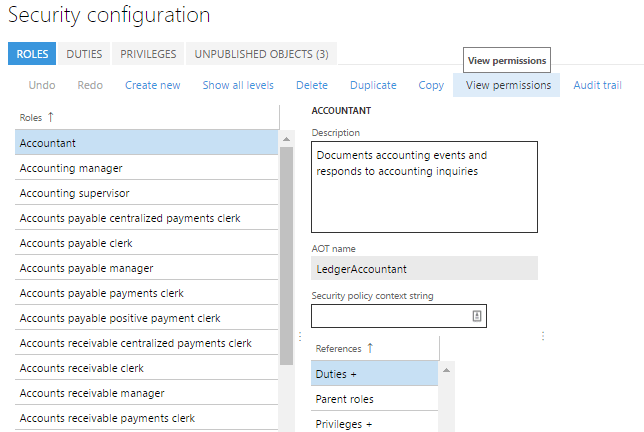
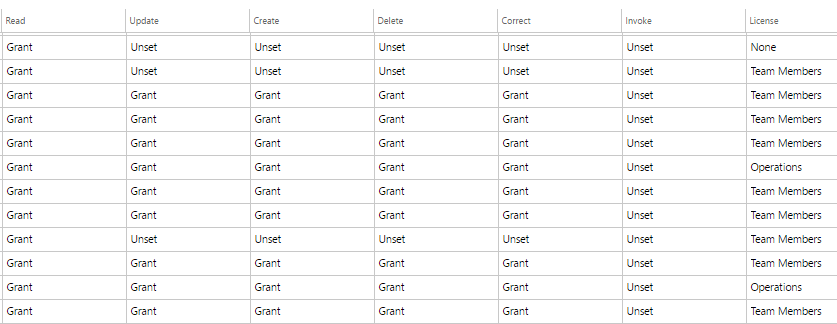
- On the System Administration -> Security Configuration page if you select a role and choose View Permissions
- You will then be presented with a report that shows an overview of the role, duty, privilege, and entry point assignment
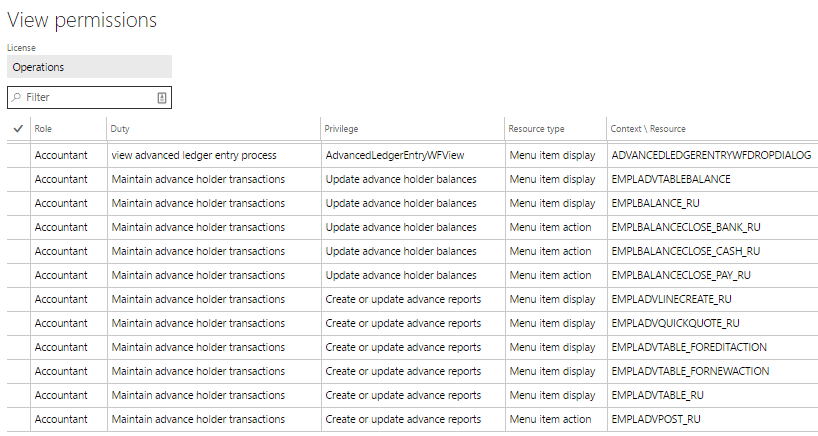
- You can also follow this process to get the same information at a duty and privilege level
- On the System Administration -> Security Configuration page if you select a role and choose View Permissions
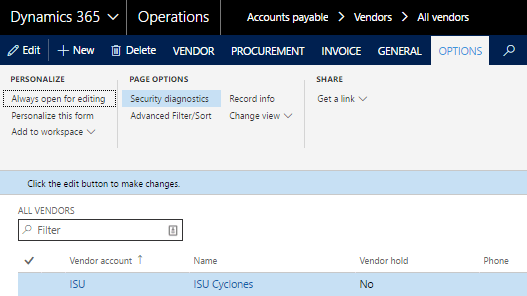
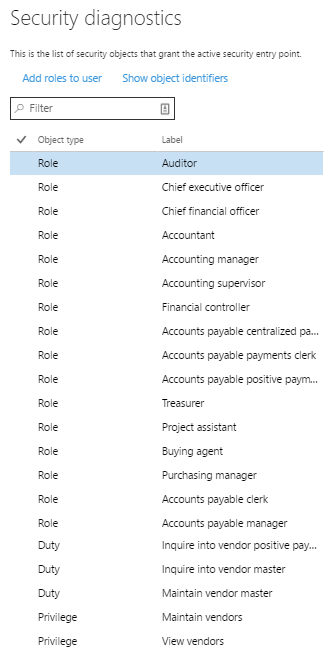
- Breakdown of the roles, duties, and privileges that have access a particular page/form in Dynamics 365 Enterprise
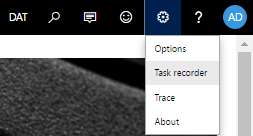
- Record a task/process
- To start recording a process go to gear in the menu bar and click on Task Recorder
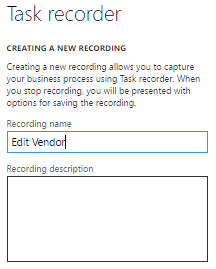
- Give the recording a name and description
- Navigate the steps required to complete the task, each step will be recorded in the right hand pane
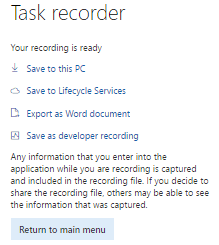
- When you are done, click the Stop button in the top menu bar and you will be presented with options to save the task steps in a number of ways
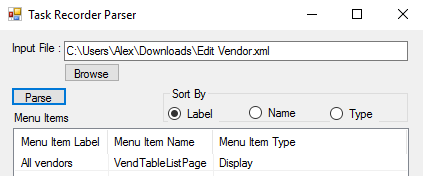
To help with the process of figuring out which menu items are used during the task, I have created a tool to help parse out a Developer’s Recording, it is available on my GitHub and a screenshot is below.
UPDATE:
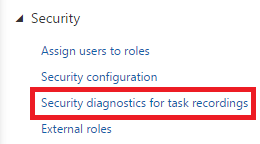
Dynamics 365 Enterprise has now added an easy way to parse the task recordings to get the menu item data from it. In the system administration module, under the Security heading you will find an entry for ‘Security diagnostics for task recordings’.
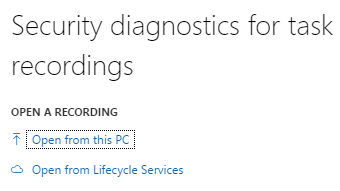
If you click on that you will be presented with a couple options, with the Open from this PC option you can upload previously downloaded task recording XML files, you can also open any saved task recording from LCS.
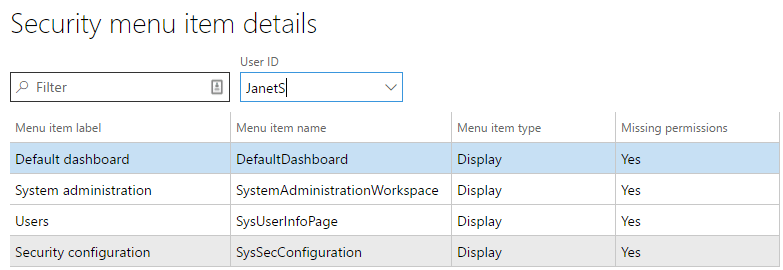
Once the file is processed, you will be presented with a screen with very similar output from the utility I wrote. It will show you the label name, AOT name, and type of each menu item found in the task recording. One really cool feature, is that you can select a user from the User ID drop down and the system will tell you whether that user currently has the necessary permissions. In the example below, you can see that this user is missing the necessary permissions to perform this process.